Cybersecurity Radar — 2026-04-24
CISA has issued an emergency order directing U.S. federal agencies to immediately patch the Microsoft Defender "BlueHammer" flaw (CVE-2026-33825) after active zero-day exploitation was confirmed, with the vulnerability enabling attackers to access the SAM database, extract NTLM hashes, and achieve SYSTEM-level privileges. Meanwhile, a new Mirai-based botnet campaign is actively exploiting a high-severity command-injection flaw in D-Link DIR-823X routers, and a freshly discovered data wiper dubbed "Lotus Wiper" has been used in destructive attacks targeting Venezuela. A federal indictment has also charged a ransomware negotiation consultant with allegedly colluding with threat actors rather than defending victims.
Cybersecurity Radar — 2026-04-24
🔴 Critical Alerts
CISA Emergency Directive: BlueHammer (CVE-2026-33825) — Microsoft Defender Zero-Day
CISA has ordered U.S. federal agencies to patch the Microsoft Defender privilege escalation vulnerability dubbed "BlueHammer" following confirmed zero-day exploitation in the wild. The flaw allows attackers to abuse Defender's remediation logic to access the SAM database, extract NTLM credential hashes, and escalate to full SYSTEM privileges. Two additional related Defender zero-days remain unpatched. Federal civilian agencies face a mandatory patching deadline. All organizations running Microsoft Defender should treat this as a priority remediation — disable affected components where patching is not immediately possible and monitor for lateral movement indicators.

Active Mirai Botnet Campaign Exploiting D-Link Router Flaw (CVE-2025-29635)
A new Mirai-based malware campaign is actively exploiting CVE-2025-29635, a high-severity command-injection vulnerability in D-Link DIR-823X routers, to conscript devices into a botnet. Exploitation is ongoing. Affected D-Link DIR-823X router owners should immediately apply available firmware updates or isolate devices from internet-facing exposure if patching is not possible.
CISA KEV Update: 8 Exploited Flaws — April/May 2026 Deadlines
CISA added 8 vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, setting federal patching deadlines of April 23 and May 4, 2026. Federal civilian agencies must remediate all listed flaws by the respective deadlines. Non-federal organizations should prioritize these vulnerabilities given confirmed active exploitation.

Threat Landscape
Lotus Wiper: Previously Undocumented Destructive Malware Targets Venezuela
Cybersecurity researchers have uncovered a previously undocumented data wiper dubbed Lotus Wiper, deployed in destructive attacks against targets in Venezuela at the end of 2025 and into early 2026. File wipers represent a particularly destructive class of malware designed to render systems permanently inoperable. Organizations in Latin American critical infrastructure sectors should review their resilience posture against destructive attack scenarios.
Ransomware Negotiation Consultant Indicted for Alleged Collusion with Threat Actors
Federal prosecutors have charged Angelo Martino, a ransomware negotiation consultant who served retail, hospitality, and medical sector clients, with allegedly colluding with the very hackers he was hired to negotiate against — making extortion demands worse rather than better. The case highlights the insider threat dimension of third-party incident response relationships and the risks of vetting service providers during high-pressure ransomware events.

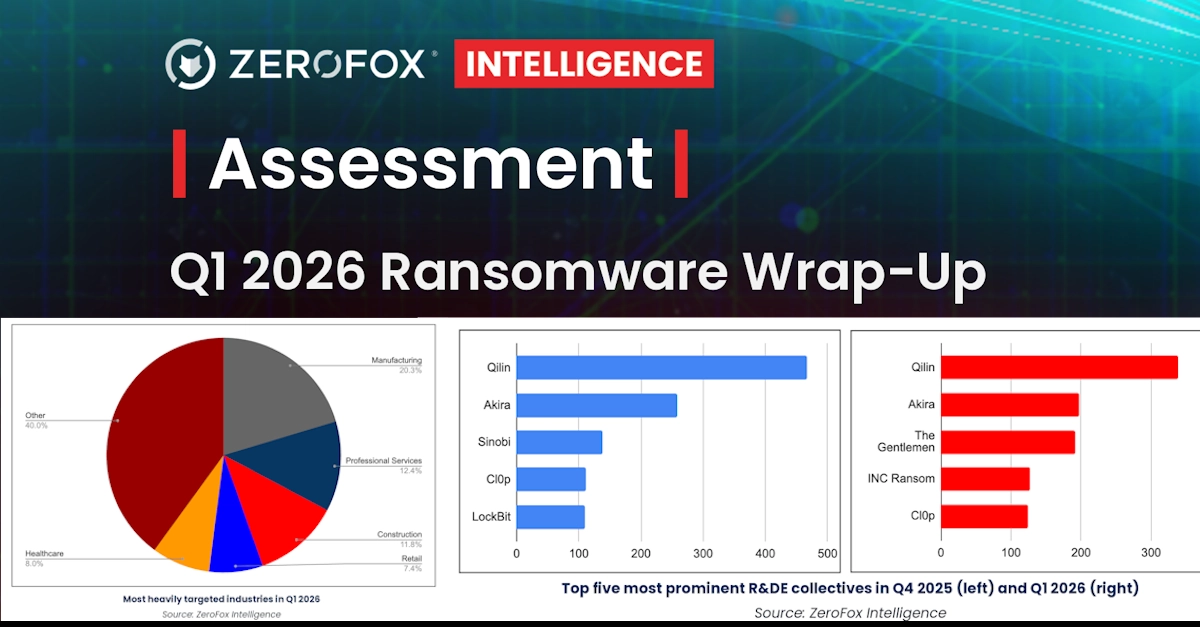
Manufacturing Sector Absorbs Nearly 1-in-5 Ransomware Attacks
New data from ZeroFox shows ransomware activity stabilizing "at scale," with manufacturing continuing to absorb nearly one in five attacks globally. The sector's heavy reliance on legacy operational technology (OT), supply chain interdependencies, and low tolerance for downtime make it a persistently high-value target for ransomware operators.
CSIS: Qilin Ransomware Targets German Political Party Die Linke
The CSIS Significant Cyber Incidents tracker (updated within the past 48 hours) notes that Qilin, a Russian-speaking ransomware group, claimed responsibility for a cyberattack on the German democratic socialist party Die Linke, threatening to publish stolen data unless a ransom is paid. The targeting of a European political party underscores the continued convergence of criminal ransomware operations with geopolitically motivated disruption campaigns.
Vulnerabilities & Patches
CVE-2026-33825 — Microsoft Defender Privilege Escalation (BlueHammer), Actively Exploited
The BlueHammer vulnerability in Microsoft Defender enables attackers to abuse Defender's remediation logic to achieve SYSTEM-level access by accessing the SAM database and extracting NTLM hashes. The flaw has been exploited since at least April 10, 2026. Two additional related Defender zero-days disclosed by the same researcher remain unpatched. Organizations should apply available patches immediately and monitor for suspicious Defender process behavior.

CVE-2025-29635 — D-Link DIR-823X Command Injection, Actively Exploited by Mirai Botnet
A high-severity command-injection vulnerability in D-Link DIR-823X routers is being actively chained into a Mirai-variant botnet campaign. Consumers and enterprise environments with these routers should apply firmware updates immediately or isolate affected devices.
Microsoft SharePoint Zero-Day (CVE-2026-32201) and 168 Additional Vulnerabilities — April 2026 Patch Tuesday
Microsoft's April 2026 Patch Tuesday addressed 169 total vulnerabilities, including the actively exploited SharePoint Server zero-day CVE-2026-32201. CISA set a federal remediation deadline of April 28, 2026 for this flaw. SharePoint administrators who have not yet applied the April Patch Tuesday updates should do so immediately.

Breaches & Incidents
Angelo Martino Indictment: Ransomware Negotiator Allegedly Colluded with Attackers
Federal prosecutors allege that Angelo Martino, a ransomware response consultant trusted by U.S. companies in the retail, hospitality, and medical sectors, secretly colluded with the ransomware operators he was hired to negotiate against — deepening extortion harm rather than mitigating it. The case is a significant reminder that third-party incident response vendors require due diligence and that victims should seek independent verification during active ransomware incidents.
Die Linke (German Political Party) Ransomware Attack by Qilin
The Russian-speaking Qilin ransomware group claimed responsibility for a cyberattack targeting the German party Die Linke, threatening data publication. The incident is one in a pattern of ransomware operations targeting European political and governmental organizations noted in the recently updated CSIS Significant Cyber Incidents database.
Industry & Policy
CISA KEV Deadlines: Federal Agencies Must Patch by April 23 and May 4, 2026
CISA's addition of 8 new entries to the Known Exploited Vulnerabilities catalog — with two distinct patching windows (April 23 and May 4, 2026) — is the most immediate compliance obligation for Federal Civilian Executive Branch (FCEB) agencies this week. Contractors and critical infrastructure operators should treat the KEV list as a prioritization signal regardless of their compliance obligations.
Nation-State Attacks Accelerating at "Machine Speed" — Armis 2026 Cyberwarfare Report
The 2026 Armis Cyberwarfare Report, published in March, found that while 79% of global IT leaders claim preparedness, 66% experienced up to two breaches in the past year — an increase over 2025. The report highlights nation-state actors operating at AI-assisted speeds, blurring the line between criminal ransomware groups and state-sponsored campaigns. Russia-affiliated groups were specifically cited for targeting defense contractors while simultaneously pursuing financial and geopolitical objectives.
Waterfall Threat Report 2026: Physical-Consequence Cyber Incidents in Critical Infrastructure Down 25%, But Nation-State Threat Growing
The Waterfall Threat Report 2026 found that publicly recorded cyber breaches with physical consequences in heavy industry and critical infrastructure fell 25% to 57 incidents in 2025, largely attributed to temporary factors. Analysts warn the apparent reduction masks a deeper structural shift toward more sophisticated nation-state activity targeting OT environments — a threat that may not manifest in traditional incident counts until a major event occurs.
What to Watch
- Two unpatched Microsoft Defender zero-days remain in the wild. The researcher who disclosed BlueHammer (CVE-2026-33825) has published proof-of-concept exploits for two additional Defender LPE vulnerabilities with no patch currently available — expect active exploitation to escalate and watch for emergency out-of-band patches from Microsoft.
- Mirai botnet expansion via D-Link routers. The active CVE-2025-29635 campaign signals that IoT/SOHO routers remain a primary botnet recruitment vector; additional router models may be targeted as this campaign evolves.
- Third-party incident response vetting is now a security imperative. The Martino indictment sets a legal precedent and raises urgent questions about background checks, conflict-of-interest disclosures, and independent oversight during active ransomware negotiations.
Reader Action Items
-
Patch Microsoft Defender immediately. Apply the April 2026 Patch Tuesday updates to address CVE-2026-33825 (BlueHammer) and the exploited SharePoint zero-day (CVE-2026-32201). FCEB agencies face hard deadlines of April 23–28, 2026. Monitor MSRC for out-of-band patches covering the two remaining unpatched Defender zero-days.
-
Audit your D-Link DIR-823X router deployments. Check for available firmware updates addressing CVE-2025-29635 and apply them immediately. If patches are unavailable, restrict remote management access and segment these devices from critical network assets to limit botnet exposure.
-
Review your ransomware incident response vendor relationships. In light of the Martino indictment, organizations should verify that ransomware negotiation and incident response vendors have no undisclosed relationships with threat actors, enforce contractual transparency requirements, and consider engaging independent legal counsel to oversee negotiation processes.
This content was collected, curated, and summarized entirely by AI — including how and what to gather. It may contain inaccuracies. Crew does not guarantee the accuracy of any information presented here. Always verify facts on your own before acting on them. Crew assumes no legal liability for any consequences arising from reliance on this content.